How to Choose the Right SaaS Backup Solution for Your Business
Ensure that your data remains secure and recoverable. As technology continues to advance, more and more businesses like yours are adopting Software-as-a-Service (SaaS) applications due to their flexibility, affordability and user-friendly nature. These [...]
The Most Dangerous Myths About Cloud Data Backup
Your cloud data is vulnerable and needs extra protection. For businesses, Software-as-a-Service (SaaS) solutions offer unparalleled opportunities to enhance efficiency, scalability and overall operations. However, growing SaaS backup-related misconceptions also have the potential to hurt your business [...]
How to Beef Up Your Incident Response Plan
Make an incident response plan now before a security breach happens. Are you prepared to face a cybersecurity breach, a natural disaster or a system failure? Such disruptive events can strike at any moment, causing chaos and [...]
Don’t Make These Incident Response Planning Mistakes
Be proactive and plan your response to a security breach. Worried about cyberattacks hitting your business? You're not alone. Cyberattacks pose a real danger to businesses like yours and without a solid incident response plan, your business [...]
The Hidden Costs of Ineffective Data Management
Data is the backbone of your business, and you can use it to generate additional revenue. In today's business landscape, data isn't just power -- it's the very lifeline that fuels business decisions, drives innovations and shapes [...]
A Deep Dive Into Data Governance
Data governance is about setting rules for managing your data. In the world of business, your data holds the key to understanding customers, market trends and internal operations. Making the most of this information is crucial for [...]
Tackling the Hidden Challenges of Network Monitoring
Is your computer network optimized? Your network is your business’s lifeline. A healthy and secure network is critical for seamless communication and operational efficiency. That’s why it’s crucial to proactively identify issues and optimize performance through continuous [...]
Bolster Cyber Defenses With Routine Security Tests
Find out if your network needs some extra care. Businesses today face a range of cybersecurity threats, from social engineering attacks like phishing to sophisticated ransomware. For business leaders like you, protecting your network is crucial since [...]
How to Ensure Your Cyber Insurance Pays Out
Fortify your cybersecurity defenses and maximize insurance payouts promptly. In the current digital environment, where cyberthreats are commonplace, it makes perfect sense to have cyber liability insurance. However, just having a policy in place doesn’t guarantee a [...]
Key Considerations When Selecting the Right Cyber Insurance Coverage
Do you know how first-party and second-party insurance coverage differ? Is your business prepared to confront today’s growing cybersecurity threats? Although adopting the latest technologies and industry trends is undoubtedly crucial, it is equally important to ensure [...]
How Effectively Managing Risk Bolsters Cyber Defenses
Cyber risk management empowers organizations to strengthen their defenses. In today’s rapidly evolving digital landscape, where cyberthreats and vulnerabilities continually emerge, it’s obvious that eliminating all risk is impossible. Yet, there’s a powerful strategy that can help [...]
How to Achieve StrategicCyber Risk Management With NIST CSF
NIST CSF empowers business leaders to boost organizational cybersecurity. Keeping sensitive data and critical tech safe from cyberattacks is crucial for businesses like yours. Your survival and growth depend on how well your organization can withstand cyberthreats. [...]
Top Misconceptions About Digital Transformation
Misconceptions about digital transformation keep businesses from achieving their full potential. Digital transformation is necessary for all businesses that want to thrive in today's competitive market. It helps businesses like yours win new customers, improve efficiency and [...]
Top Technologies Driving Digital Transformation
The survival of your business hinges on having a digital transformation strategy. When creating a budget for your business, it’s important to remember that technology costs are more than just operational expenses. They should be considered an [...]
A Deep Dive Into Phishing Scams
Email safety measures function as a safety net, averting unfortunate incidents. Phishing scams remain one of the most prevalent and successful types of cyberattacks today, so being aware of the danger they pose to businesses like yours [...]
How Social Media Misuse
Can Harm Your Business
Let us help you navigate the intricate realm of social media threats. Social media has significantly transformed the way we communicate and do business. However, this growing popularity also comes with potential risks that could cause harm [...]
Be Aware of These Top AI Cyber-Risks
Let’s build an innovative and responsible AI-powered future. The rise of AI has sparked a revolution. Everyone, from industry giants to smaller enterprises, is captivated and eager to leverage AI’s endless possibilities. However, [...]
Don’t Forget Cybersecurity in Your Emergency Preparedness Plan
Secure your business from potential disasters and their consequences. A disaster preparedness plan helps businesses withstand any calamity. However, many businesses are unaware that a cybersecurity strategy is also crucial for building a robust disaster preparedness plan. [...]
Four Ways Disasters Fuel Cyberattacks
Disasters open the door to cybercriminals. Safeguard what you’ve worked so hard to build. Your business, in all likelihood, already faces numerous challenges in today’s tech-driven world. However, the aftermath of an unexpected disaster can push your [...]
Why Your Business Needs to Beef Up Employee Security Awareness
Proactively mitigate risks and empower your workforce to defend against cyberattacks. We live in an era where organizations are increasingly aware of the ever-changing cybersecurity landscape. Despite billions of dollars invested worldwide to fend off cyberthreats, cybercriminals [...]
Don’t Sabotage Employee Cybersecurity Training With These Common Mistakes
Create a culture of security awareness that empowers employees. In today’s rapidly evolving threat landscape, employee cybersecurity training is crucial. It acts as the frontline defense against cyberattacks, empowering your workforce to identify and mitigate potential threats. [...]
Don’t Let These Outsourced IT Myths Limit Your Success
Increase Your Business Success With Outsourced IT. In today’s fast-paced and digitally driven world, the demands placed on the IT infrastructure of businesses like yours are ever-increasing. To meet these challenges head-on, embracing outsourced IT services and [...]
What to Look for in an Outsourced IT Partner
Is your business technology holding you back? In today’s digital age, most businesses rely heavily on technology to streamline their operations and stay ahead of the competition. However, managing an entire IT infrastructure in-house can be overwhelming [...]
Get Ready for CMMC Requirements Now
Learn steps to compliance with DFARS and new CMMC 2.0 requirements. Anyone offering a sure-shot solution to all your Cybersecurity Maturity Model Certification (CMMC) woes is trying to pull a fast one on you. The CMMC is [...]
The Interim DFARS Rule and What It Means for You
Now is the time to conduct an accurate DFARS self-assessment. The Cybersecurity Maturity Model Certification (CMMC) was formally made part of the Defense Federal Acquisition Regulation Supplement (DFARS) in January 2020 and updated to CMMC 2.0 in [...]
How to Stay Ahead of AI-Powered Cybersecurity Risks
Improve your preparedness against AI-powered cyberattacks. While artificial intelligence (AI) has many benefits for businesses, it has also created new vulnerabilities that cybercriminals can exploit to carry out complex cyberattacks that are difficult to detect and mitigate. [...]
How to Successfully Leverage AI in Your Business
Four key actions you should take to avoid roadblocks. Artificial intelligence (AI) can help organizations like yours gain an edge in today's highly competitive business landscape by increasing efficiency, productivity and profitability. You can [...]
3 Steps to Zero Trust Cybersecurity for Small Businesses
Cyberattacks have become rampant and have also grown in sophistication. A simple lapse in your network security could lead to a chain of events that could prove catastrophic for your business. You can avoid this by implementing [...]
Don’t Trust These Zero Trust Security Myths
Four common myths surrounding the zero-trust framework In today’s threat landscape, where businesses are constantly at risk of being targeted by a cyberattack, adopting a zero-trust security model could be a wise decision from a cybersecurity point [...]
Top 9 Benefits of Outsourcing Your Cybersecurity
There are a lot of benefits to outsourcing your cybersecurity When it comes to protecting your business from cyberthreats, having the right tools and technology is only half the battle. You also need the expertise, controls and [...]
It’s Time to Bust These 4 Ransomware Myths
Ransomware attacks are becoming increasingly frequent. With cybercriminals constantly evolving their tactics and targeting businesses of all sizes, organizations like yours must proactively safeguard your data and systems. In today’s digital age, ransomware [...]
The Best Defense Against Ransomware
Ransomware attacks will only continue to increase & expand. Ransomware is a type of malicious software that encrypts files on a device or network, making them unusable until the victim pays the attacker a ransom. What started [...]
Defense in Depth (DiD): Think Like a Hacker
Stay informed about the changing threat landscape. Cybercriminals are always looking for new ways to bypass security defenses. That’s why it’s essential to think like a hacker and adopt measures to stay ahead of them. This is [...]
Stepping Up Your Cybersecurity with Defense in Depth (DiD)
Cybersecurity is an essential aspect of any business or organization. As technology evolves, so do the threats that can harm an organization’s operations, data and reputation. One of the most effective ways to defend against these threats [...]
Does Your Business Need Co-Managed IT?
When it comes to managing your business’s IT infrastructure, there are several options available. One is fully managed IT, where an IT service provider takes care of all aspects of your IT needs, from monitoring and maintenance [...]
Top 4 Co-Managed IT Myths
As a business owner, you may feel that you need to choose between relying on your in-house IT staff or outsourcing technology management to an IT service provider. There is, however, a third option: co-managed IT. This [...]
Minimizing Cyber Supply Chain Risks through Effective Vendor Selection
As a business owner, it's crucial to prioritize the security of your supply chain and choose vendors that are committed to implementing best-in-class defense measures. This is because supply chain attacks can exploit weaknesses within your supply [...]
Top 3 Supply Chain Risk Misconceptions
Supply chain attacks are a primary concern for businesses nowadays. With technology becoming increasingly advanced, businesses like yours must ensure there are no vulnerabilities in the supply chain. Unfortunately, many companies still believe [...]
How to Effectively Manage Supply Chain Risks
There are many benefits digital transformation has brought to businesses like yours, such as easier inventory management and order processing. However, it does make organizations more vulnerable to cyberattacks and data breaches. A breach occurring anywhere in [...]
Recommended Best Practices to Reduce Cyber Supply Chain Risks
What exactly is a supply chain attack and how does it impact your organization? A supply chain attack is a type of cyberattack that targets an organization’s external suppliers and vendors. This can have significant consequences for [...]
Did you know hardware and software expire too?
We are all aware of the term “use by date.” It is regularly used when talking about food and medications and refers to the date after which the product is no longer safe to consume. However, did [...]
3 Technology End-of-Service Myths
It's crucial to keep all software and hardware up to date to maintain optimal security. If you don’t, cybercriminals can easily infiltrate your network and the chances for downtime increase significantly. However, many businesses don't realize that [...]
4 Practical Steps to Take When Hardware and Software Expire
When a software or hardware product reaches its End-of-Life (EoL) or End-of-Service (EoS), it's no longer supported by the manufacturer. This can be a cause of concern for organizations like yours because unsupported technologies have no routine [...]
The Dangers of Running Outdated Software
Your software is only as good as its last patch. Reaching End-of-Life (EoL) or End-of-Service (EoS) means critical patches and updates are no longer available, leaving you vulnerable to various problems. Some make [...]
4 Core Benefits of Cloud Backup for SaaS Platforms
Businesses like yours are increasingly adopting cloud-based solutions to keep up with the rapidly changing technological landscape. According to a recent study by Gartner, cloud adoption will not slow down anytime soon. Many of these organizations, [...]
Myths About Business Cloud Backup Platforms
Your data is essential for your business's success. There’s no doubt about it in the modern digitized era. However, not having a backup for your cloud-based service provider can result in the loss of this valuable [...]
4 Practical Steps for Vendor Cloud Backup
When you entrust your business data to a cloud-based platform, you expect it to be safe and sound. However, most cloud platforms like Microsoft 365, Google Workspace, and Salesforce acknowledge their backup shortcomings and recommend having [...]
99 Problems but Cloud Backup Isn’t 1
Data loss is a genuine threat to all businesses. Not only can it cost a lot of time, money, and other resources to fix, but it can also be a huge pain to deal with when [...]
How an IT Service Provider Can Simplify Budgeting for Small Businesses
Do you find budgeting for IT challenging? If so, you aren’t alone. While the IT budgeting process can be tricky for small businesses, it can be especially difficult for those trying to do it all by themselves. With [...]
Don’t Overlook These 3 Technology Budget Categories
Are you considering all the necessary technology categories when planning your annual budget? Technology is essential for any modern business such as yours, but it’s easy to focus solely on routine services that keep the lights on. This [...]
4 Common Technology Budgeting Mistakes
Are you planning to include your IT needs in your annual budget this year? If so, congratulations! You're doing something incredible to ensure your small business’ success. Budgeting for technology can be tricky. On the one hand, you [...]
Tech Budgeting 101 for Small Businesses
With the new year around the corner, now is an excellent time to review your organization’s budget to ensure your business has the resources it needs to continue to grow and prosper in the coming year. It’s important [...]
Busting Four Popular Cybersecurity Myths
As the business world becomes increasingly digitized, you’ll have to tackle several dangers that come with doing business online. Cybercriminals nowadays have several methods to target organizations, from credential hacks to sophisticated ransomware attacks. This is [...]
4 Employee Cyberthreat Traits
To succeed in today’s modern competitive business landscape, you need to understand the strengths and weaknesses of your employees. This will equip you to identify areas where employees may need further training, including cybersecurity awareness. Are [...]
4 Cyberthreats Small Businesses Need to Know
Data breaches have become more common in recent years, owing primarily to the rapid emergence of new threats. According to a new study, the average cost of a data breach increased 2.6% from 2021 to 2022. [...]
Why Passwords are Your Business’s Weakest Point
In today's digital world, safeguarding your organization's online assets is critical. Unfortunately, poor password hygiene practices by some employees cause problems for many small businesses, leaving them vulnerable to hackers. Cybercriminals are constantly trying to find [...]
3 Times Businesses Were Denied Cyber Insurance Payouts
Cyber insurance is a type of insurance that protects businesses from financial losses that can result from a cyberattack. While it’s an essential tool for businesses of all sizes, there are some facts you should be [...]
3 Types of Cyber Insurance You Need to Know About
As the world becomes more digitized and cybercrime increases, the need for cyber insurance is something businesses should not overlook. If your company handles, transmits or stores sensitive data, you need to know about cyber insurance. [...]
How an IT Service Provider Can Help With Cyber Insurance
When looking for cyber insurance for your small business, you may find it hard to navigate technology and insurance jargon. There are even different types of cyber coverage and you might not be sure what you [...]
Don’t Fall for These Cyber Insurance Myths
As the world increasingly moves online, so do the risks to our businesses. Cyber insurance is one way to help your business recover following a cyberattack. It covers financial losses caused by events such as data [...]
Why Your Business Needs to Prepare for Cyber Incidents
As the world becomes more digital, so do the risks of conducting business online. Cyber incidents can happen to any business, regardless of size or industry, and can have serious consequences. The following are some examples [...]
Cyber Incident Response 101 for Small Businesses
Imagine it's the end of a long workday and you're ready to head home for the evening. However, just as you're about to leave, you find out your email credentials have been hacked and critical data [...]
Balancing a Proactive and Reactive Approach to Cyber Incidents
A cyber incident is a type of security event that can harm a business like yours. Ranging from data breaches and system failures to malware attacks and phishing scams, these incidents can hinder productivity, revenue growth, [...]
Cyber Incident Prevention Best Practices for Small Businesses
As a small business owner, you may think you are “too small” to be the target of cybercrime because you aren’t a large, multimillion-dollar company. However, this couldn’t be further from the truth. Although the media [...]
What a Top-Notch IT Services Provider Will Offer Your Business
There are several reasons why small and medium-sized businesses (SMBs) like yours should be able to meet all their technology needs in one location. One reason is that small businesses often lack the resources of large [...]
Why Smart Businesses Outsource Their IT Needs
In today's business world, technology plays a significant role in almost every industry. It has disrupted the way we live, work, interact and collaborate. There are endless ways that technology can benefit businesses like yours. Technology [...]
Need More Reliable IT Services for Your Business?
One of the biggest challenges that small and medium-sized businesses (SMBs) face is how to use their limited resources most effectively. Every decision, from what products or services to offer to how to market and sell [...]
How to Find the Right Managed IT Service Provider for Your Business
When looking for an IT service provider for outsourced tech support, it’s crucial to remember not all IT service providers are the same. You need to find one that understands your specific needs and can offer [...]
How to Build Trust Using Your SMB’s Technology
Technology can be a daunting investment for small and medium-sized businesses (SMBs). Between the initial cost and the time and effort it takes to maintain and keep up with technology, it’s little wonder why so many [...]
What to Say ‘No’ and ‘Yes’ to When Practicing Trust-Building in Your Business
The world has become a less trusting place. A recent study by the Edelman Trust Barometer found that trust in business, media, government and NGOs has reached an all-time low. The study also revealed that trust [...]
The Case for Trust-Building as a Small Business (It’s Not Just for Enterprises)
There is a strong connection between trust and prosperity. In fact, when trust levels are high, businesses tend to grow faster. According to McKinsey and Company, Harvard Business Review, Forrester Research and many other reputable organizations, [...]
Why SMBs Need to Prioritize Trust
While you would not expect a technology company to discuss topics such as trust, we're not like most managed service providers (MSPs). We understand how technology affects trust and impacts your people, processes and bottom line. [...]
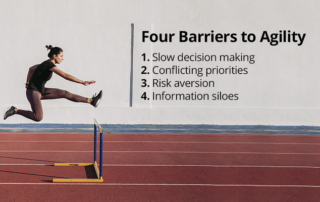
Agility for Your People, Processes and Technology
Nothing is more crucial to a business than stability. Yes, profit matters, but companies can achieve consistent profits easily when markets are stable. The world, of course, doesn’t always work this way. Markets are highly unpredictable [...]
Making the Case for SMB Agility
The last two years have been a bumpy ride for organizations of all sizes globally. During this time, small and medium-sized businesses (SMBs) were hit the worst. Since most SMBs have limited cash and resources, setbacks [...]
Things to Avoid While Practicing Organizational Agility
Even though it’s no secret that small to medium-sized businesses often have vastly fewer resources in comparison to larger enterprises, prioritizing agility is just as critical for their survival. This is because, in today's world, where [...]
What is Organizational Agility?
It's hard to predict the future. Just think of all that has happened in the world in the last two years. From the COVID-19 pandemic to supply chain issues to inflation and war, no one could [...]
What Does It Mean to Build a Sustainable Business?
Being a sustainable business means more than just recycling and using renewable energy. It means laying the groundwork for future employee and customer growth. An organization with sustainability as one of its core principles has a [...]
Common Scalability Mistakes SMBs Make
Most small and medium-sized businesses (SMBs) are stretched for time and resources, due to which they may end up rushing through process implementations, technology upgrades and new hire training. Inevitably, this results in botched executions and [...]
Top Technologies for Scalability
Rushing through process implementations, technology upgrades and new hire training can cause botched executions and unnecessary confusion. That’s why businesses must pursue a sustainable strategy that allows them to grow smarter, not just faster. Sustainability in [...]
Aligning People, Processes and Technology to Scale
Your company operates in a turbulent business environment where new technologies are reshaping industries, customer preferences are evolving rapidly and geopolitical equations are shifting dramatically. If you’re struggling to adapt to these quick and challenging transitions, [...]
3 Common Tech Acceleration Mistakes
As a business executive, you often face the task of keeping up with current technology trends to boost productivity, lower expenses, strengthen your brand value, enable new collaboration, and maximize profitability. If you want to [...]
Top Tech Acceleration Technologies for 2022
Organizations have had to make several overnight adjustments to stay afloat over the last few years. If you’re like most businesses, you may have needed solutions to support remote work and collaboration. But are those [...]
Why Smart Tech Acceleration is Essential to Long-Term Business Growth
In your attempt to adapt to the evolving technology landscape and the onset of the COVID-19 pandemic, have you invested in solutions that may not be assisting your company in achieving its long-term goals? If [...]
5 Elements of Effective Tech Acceleration
Are you up to date with the current technology landscape? Do you have an idea of what it will look like in the next five to 10 years? Knowing this information is crucial as it can [...]
Why Apply Change Management Principles to Your Technology Upgrade
The technological landscape has advanced dramatically over the last couple of decades and continues to move faster than anyone could have ever imagined. Failure to keep up with the latest technology trends and current business practices can put your [...]
6 Questions to Ask Before Implementing a Technology Change
It can be exciting to introduce new technology into your business. Finding a solution that will help your team members do their jobs more efficiently and effectively by filling a gap in your technology infrastructure is certainly an achievement. [...]
4 Common Setbacks With Ineffective Technology Change Management
Technology is advancing at an unprecedented pace, empowering businesses to accomplish more in less time. The transformations that technology has brought about in the business world are mind-boggling and with transformative change comes stress. Without a defined change management [...]
Change Management Basics for Technology Refreshes
Once you've completed a technology audit and prioritized the order in which you'll close gaps in your infrastructure, it's critical to remember that there are actions you must take prior to implementation for change to be successful and well-received [...]
Top 4 Tech Trend Predictions for 2022
Over the last few decades, technology has been a driving force in business transformation and doesn't show any signs of slowing down. The fact that direct digital transformation investments are projected to total $7 trillion between 2020 and 2023 [...]
How to Prioritize Your Technology Gaps
Today's technology-based businesses must deal with multiple issues, including cyber threats, head-to-head competition and regulatory compliance. Hence, keeping your technology infrastructure up to date is critical, and a technology audit is the best place to start. A technology audit [...]
Why You Should Prioritize Your Technology Gaps
Technology is an unavoidable component of most businesses these days, helping them achieve their goals and vision. However, if you are not cautious, technological flaws could allow cybercriminals to access your network and cause harm to your company. Technology [...]
6 Signs You Need a Tech Refresh
When used strategically, technology can help small and medium-sized businesses (SMBs) develop a more productive, efficient and innovative workforce. That’s why businesses that prioritize technology are three times more likely to exceed corporate goals.* In a business world that’s [...]
4 Reasons to Refresh Your Technology Infrastructure in 2022
After the ups and downs of the last year and a half, the business world is making its way into 2022 with renewed optimism. Business executives are contemplating strategies to start the year with a strong quarter by adapting [...]
3 Benefits of Conducting a Technology Audit
When was the last time you conducted a comprehensive technology audit? If it's been a while or hasn't happened at all, you're probably vulnerable to a cyberattack. Cybercrime shows no signs of slowing down and is expected to cost [...]
How to Become a Resilient Organization
The last year and a half have taught us that the world can experience a tremendous change in a short time. Whether it’s rapid technological advancements, cyberattacks, stalling economies or even a global pandemic, only resilient organizations can weather [...]
Is Your Supply Chain Resilient?
The major upheavals of the last couple of decades, such as the global recession and the COVID-19 pandemic, have demonstrated that firms will suffer severe setbacks if their supply chains are not resilient. An entire supply chain becomes vulnerable [...]
A Resilient Organization Starts with Cyber Resilience —Here’s Why
Global events, such as recessions and pandemics, create enormous social and economic challenges that impact organizations and their management. From employee and customer satisfaction to financial difficulties, supply chain disruption and skyrocketing cyberattacks, top-level management oversees a wide range of [...]
What to Include in Your Incident Response Plan
A security incident can topple an organization's reputation and revenue in a short amount of time. As billionaire Warren Buffet once said, "it takes 20 years to develop a reputation and five minutes to ruin it." Keeping that in [...]
What You Should Know if Your Business Is Targeted by Ransomware
It may not be news to you that ransomware is on the rise, but the numbers may leave you shocked. In 2020 alone, there were close to 300 million ransomware attacks worldwide. The cost of ransom payments demanded by [...]
Cybersecurity: What Every Business Owner Should Know
While organizations and workers have certainly benefitted from the advancement of technology, it has also introduced an unprecedented number of cybersecurity risks. Ransomware attacks, for example, hit businesses every 11 seconds in 2021. Therefore, if you want your business [...]
PCI-DSS Compliance: What You Should Know
Over the last year, many organizations struggled to keep their private data secure against cyberthreats as they rushed to adapt to pandemic-inspired shifts in workforce and operations. Cybercrime is becoming increasingly prevalent, and the sophistication and volume of cyberattacks [...]
The Role of Compliance in Cybersecurity
The overall technology landscape is evolving at a breakneck pace. While these changes are meant to improve the quality of life, the unfortunate flip side is an increase in cyber threats. This is why global cybersecurity spending increased from [...]
4 Data Backup Myths You Need to Know About
Humans generate 2.5 quintillion bytes of data every day. That is a substantial amount of information. However, failing to keep up with the ever-changing threat landscape might wipe your share of this data in the blink of an eye. [...]
Think Beyond Basic Backups to Tackle Ransomware
Although ransomware has long been a serious concern for business owners all over the world, the COVID-19 pandemic has created new opportunities for this threat to flourish, and the attack vector is likely to become even more dangerous in [...]
Defense in Depth (DiD): Think Like a Hacker
The current threat landscape is rapidly advancing, with cybercriminals constantly upgrading their toolset to break through security defenses. If you want to outsmart malicious hackers, it’s time to start thinking like them. Fend them off with various layered defense [...]
Data Deduplication Best Practices for Hybrid Workforce
Data hygiene, from a hybrid workforce perspective, aims at the structuring of information and the elimination of dirty data from your network. It involves the implementation of sound policies to check records for accuracy and the removal of errors. [...]
The Role Deduplication Plays in a Data Cleansing Strategy
In today’s digital era, where humans produce close to 2.5 quintillion bytes of data every day, dirty data is a concern for businesses irrespective of size and industry. This is because any organization that handles duplicate, inaccurate and outdated [...]
Stepping Up Your Cybersecurity With Defense in Depth (DiD)
When the pandemic hit, businesses all over the globe had to shift to remote work almost overnight. Now, with the vaccine rollout in full swing, the hybrid work model is gaining popularity. This allows employees to work from home, [...]
5 Security Risk Analysis Myths in the Healthcare Industry
The COVID-19 pandemic threw multiple challenges at the healthcare industry. The sector saw a steep increase in demand that led to the collapse of health infrastructures in different parts of the world. What’s more, the industry experienced an unprecedented [...]
Managed Compliance as a Service May Be the Answer to Healthcare Compliance Challenges
The healthcare industry has been going through a difficult phase. While the COVID-19 pandemic overwhelmed health infrastructures across the globe, cyberattacks targeting the industry are skyrocketing. In 2020, healthcare was the worst affected industry by cybercrimes. Experts suggest that [...]
4 Reasons Cybersecurity Attack Surfaces Are Expanding
The COVID-19 pandemic impacted individuals and businesses all over the world in one way or another. Almost overnight, it disrupted the way people went about their daily routines and how companies operated. Amidst all the chaos, changes to the [...]
How Data Compliance and Cybersecurity Differ
When you run a business, compliance and security are two essential factors. Both are equally important for the seamless operation of your business. While compliance helps your business stay within the limits of industry or government regulations, security protects [...]
Why Attacks on Critical Infrastructure Are Dangerous
Critical Infrastructure (CI) comprises physical and cyber assets vital for the smooth functioning of societies and nations across the globe. The sectors that make up critical infrastructure differ from one country to another. For example, the USA considers 16 [...]
8 Elements of a Business Impact Analysis (BIA) for Compliance
A compliance program aims at protecting an organization from risk. The purpose of corporate compliance programs is to ensure that a business complies with laws or regulations relevant to it. You could consider a Compliance Program to be a [...]
Recovery Assurance (RA): Is Your Business Data 100% Recoverable?
Ever since the start of the COVID-19 pandemic, the concept of Disaster Recovery (DR) has received unprecedented attention. Most businesses have realized the importance of bouncing back quickly from a disruptive event. In 2020, about 80% of SMBs reported having [...]
The Importance of Business Impact Analysis (BIA)
As the name signifies, a BIA quantifies the impact of a cyber disruption on your business. It doesn’t matter if the disruption happens because of an internet outage or a severe breach — a BIA covers it all. A [...]
How to Build a Security-First Culture That Empowers Your Hybrid Workforce
Tools are only as good as their users. This should be your guiding philosophy as the world shifts to a hybrid work model to deal with the complexities posed by the COVID-19 pandemic. While it’s great to define and [...]
Make Hybrid Work Environments Secure
The COVID-19 pandemic caused an unprecedented shift in the way people work. Although most companies relied on a fully remote work model initially, the vaccine rollout has led to the popularization of hybrid work environments. A hybrid work environment [...]
Why You Must Comply With Your Cyber Liability Insurance
If you think that your cyber insurance claim will be cleared with no questions asked, think again. While reviewing your claim, your cyber insurance provider will assess whether you took “due care” to protect your business from being compromised [...]
The Beginner’s Guide to Cyber Liability Insurance for Business
The COVID-19 pandemic has impacted everyone in one way or another. If there is one category that most benefited from the pandemic, it’s cybercriminals. That’s why cybercrime has shot up by almost 300% since the start of the pandemic1 [...]
Why to Adopt a Comprehensive Backup and BCDR Strategy
Being a business owner is challenging. You have to deal with multiple problems at once and effectively solve each of those. You also need to have the foresight to arm your business with the right tools and solutions to [...]
Data Loss Disasters Come in Many Forms
If we’ve learned anything from the COVID-19 pandemic, it’s that we don’t have it all figured out. Not only are we vulnerable as a species, but so are the systems, processes and devices we’ve built. Natural and human-made disasters [...]
Top 9 IoT-Related Security Threats Businesses Face
The Internet of Things (IoT) is rapidly changing the technology landscape as we know it. Businesses worldwide are leveraging IoT for benefits such as seamless collaboration, access to comprehensive data and the ability to make stronger business decisions based [...]
Operational and Data Integrity Risks of IoT for SMBs
The continued rise in the number of Internet of Things (IoT) connected devices has brought about a host of security challenges for many businesses. As manufacturers compete in a race to bring their IoT devices to market, most fail [...]
Top 5 Threats IoT Devices Pose to Data Protection & Privacy
Gartner Inc. predicted that by 2023, CIOs would be responsible for over three times the endpoints they were responsible for in 2018 due to the rapid evolution of IoT trends and technologies. With billions of physical devices worldwide connected [...]
Regulations for Securing the Internet of Things
We are living in the era of Digital Transformation and witnessing first-hand the proliferation of assistive technologies such as the Internet of Things (IoT). It is estimated that the global count of IoT devices will reach around 80 billion [...]
Why Your SaaS Data Needs Backup Protection
Software-as-a-Service (SaaS) applications are more in use than ever before. Almost every company uses either one or the other SaaS application on a daily basis. The global SaaS market size is expected to reach $185.8 billion by 2024 as businesses move online and adapt to [...]
Business Continuity Plan 101
If you want your business to remain competitive even during a business disruption, you need to self-reflect. What’s your plan against the unexpected?The truth is, numerous threats can halt your business operations at any time. If your employees cannot quickly [...]
Adopt Zero Trust Security for Your SMB
With the cyberthreat landscape getting more complicated with every passing minute, cybersecurity deserves more attention than ever before. You can no longer put all your faith and trust in applications, interfaces, networks, devices, traffic and users. Misjudging and misplacing [...]
How Can Cyber Resilience Protect SMBs?
Small and Medium Businesses (SMBs) usually invest less in cybersecurity, making them easier targets for cybercriminals. Close to 30% of businesses experience a cyberattack at least once per week.1 The need for constant vigilance and defense against hackers has [...]
Prioritize Compliance for Your Business
One of the many challenges you probably face as a business owner is dealing with the vague requirements present in HIPAA and PCI-DSS legislation. Due to the unclear regulatory messaging, “assuming” rather than “knowing” can land your organization in [...]
A ‘Compliance First’ Mindset Limits Liabilities for SMBs
By adopting a Compliance First strategy, when choosing solutions and vendors, you will identify those that do not comply with your requirements, eliminate them from your selection process, and then select from the rest. It also means evaluating your [...]
Backup and Disaster Recovery: A Must-Have
Experts estimate that humans produce 2.5 quintillion bytes of data every day.1 That is a lot of information. However, having a poor backup strategy can wipe out all or vast portions of your data in a single click. From [...]
Navigating Backups and Training During Unprecedented Times
The surge in cybercrimes against businesses during the COVID-19 pandemic proved how flexible nefarious cyber players are, ready to twist and turn according to a situation to make profits out of a business’ failure. Remember that it could happen to [...]
Making Security Awareness Second Nature
Your business’ security program must start with your employees and strong security policies rather than entirely depending on your IT team or the latest security solutions. You can significantly reduce the likelihood of a data breach by combining a well-drafted [...]
The Interim DFARS Rule and What It Means for You
The Cybersecurity Maturity Model Certification (CMMC) was formally made part of the Defense Federal Acquisition Regulation Supplement (DFARS) in January 2020. The decision sent over 300,000 members of the defense industrial base (DIB), mostly small and midsize businesses (SMBs), into [...]
Why Security Awareness Training Is Essential for Backups
According to IBM’s 2020 Cost of Data Breach Report, human error causes nearly 25 percent of data breaches, meaning that a negligent employee can become a tangible threat to your business’ invaluable data. The only way to prevent your [...]
Your Biggest Cybersecurity Risk: Your Employees
Cybercriminals work round the clock to detect and exploit vulnerabilities in your business’ network for nefarious gains. The only way to counter these hackers is by deploying a robust cybersecurity posture that’s built using comprehensive security solutions. However, while you’re [...]
Are Your Business Partners and Vendors Potential Security Weak Links?
A modern supply chain consists of people, systems and technologies that enable the delivery of goods and services to end users. However, this dependency on third-party business partners opens doors to many security risks. A lot can go wrong [...]
The Top Supply Chain Vulnerability: People
The supply chains of this digital era are long and complex, and any disruptions caused by security threats will have a massive impact on the entire organization. While supply chains are prone to different types of external risks, such as [...]
How to Effectively Manage Supply Chain Risks
Digital transformation has made many things easier for businesses, right from inventory management and order processing to managing financials. On the flip side, however, it has also made companies more vulnerable to cyberattacks and data breaches. A breach occurring [...]
Regulations and Standards Governing Your Supply Chain Management Obligations
Irrespective of the size of your supply chain, you must ensure that it isn’t the reason your business is non-compliant with the necessary regulations and standards. Yes, it involves a great deal of continued effort, but it’s worth it. [...]
Regulations & Reputations: How Compliant Is Your Supply Chain?
With both technology and tech-related threats evolving faster than ever before, supply chain risks have taken on a new meaning in today’s digital world. While traditional supply chain risk management revolved around factors such as strategy, market reality and [...]
Recommended Best Practices for a Secure Supply Chain
Your business’ cybersecurity posture must prioritize detection, evaluation and mitigation of risks posed by your supply chain. It is vital that your security is upgraded on a regular basis to better prepare for any worst-case scenarios. Having said that, it [...]
Defense Strategies to Combat Insider Threats
Insider threats are among the most dangerous cyberthreats out there. Yet, organizations of all sizes seem to be either reluctant or negligent when it comes to fighting them. Over 50 percent of organizations don’t have an Insider Risk Response [...]
Insider Threats: Spotting Common Indicators and Warning Signs
Data protection regulations require your business to assess all possible threats to the sensitive data your business stores or manages. While most businesses tend to focus most of their attention on external threats, they often overlook insider threats that [...]
Potential Risks That Insider Threats Pose to PII
Personally Identifiable Information (PII) refers to any information maintained by an agency that can be used to identify or trace a specific individual. In other words, it includes data points, such as social security number, date of birth, mother's maiden [...]
How Disgruntled Insiders Pose a Serious Threat to Your Business-Critical Data
Merely mitigating external cybersecurity threats isn’t enough when it comes to fighting cybercrime in today’s ever-evolving threat landscape. Although insider threats can be as devastating and as deadly as their external counterparts, most businesses fail to track and manage [...]
Protecting Your Business-Critical Data From Human Threat
Although the technology-driven era we live in has made information sharing and data access very efficient, it has also brought forth a new set of challenges. One of the major challenges businesses face in this day and age is [...]
The Dangers Within: Understanding Insider Threats
The year 2020 witnessed an unprecedented onslaught of cybersecurity threats across the world as the global workforce underwent a forced transition to remote working. However, not all cybersecurity threats come from the outside. In a study conducted by Bitglass, [...]
Importance of Secure Cloud Backup Solution for Remote Users
In today’s world, businesses gather, analyze and process large volumes of digital data on an everyday basis. From identifying common customer behavior to creating campaigns that target the right audience, business data plays a critical role in the everyday [...]
New Year, New Risks for IT & Data Security
The COVID-19 pandemic has changed everything about the world as we know it. Just as we started embracing new practices like sanitizing, social distancing and remote working, the pandemic has also forced us to embrace systemic changes in the ways [...]
Securing Company Data With a Remote Workforce
In 2018, BlueFace predicted that remote work would start competing with office work by 2025. Little did they know that the pandemic would accelerate this process tenfold. Businesses were thrown into the deep end when they had to suddenly [...]
Prioritizing Compliance Commitment Across All Work Environments
A secure and compliant work environment is what data protection regulations worldwide mandate your business to build and maintain. It must be secure enough to mitigate as many risks as possible and be compliant with every single rule/guideline listed in [...]
Required Data Security Controls for Compliance
No data protection regulation anywhere in the world expects your business to have a 100 percent perfect plan for fighting cybersecurity threats. However, your business is definitely expected to install all the necessary checks and balances that make up a [...]
Regular Backup Testing: Save Time, Money and Energy
As a business owner, you’re probably already aware of the threats looming over data security in today’s digital environment. The irretrievable loss of critical business data could be the worst thing to happen to your business. Apart from the [...]
First Step to Compliance: A Thorough and Accurate Risk Assessment
Complying with data privacy and protection regulations wouldn’t give several business owners sleepless nights if it only meant installing a predefined list of security solutions. Compliance goes way beyond this and for good reason. In principle, regulators, local or international, [...]
Monitor, Test, Restore – Making Sure Your Backups Are Ready!
Backups play a critical role in any data protection strategy. If you are counting on your backups for disaster recovery and business continuity, unexpected backup failure can prove to be disastrous for your business. Especially when backups are scheduled [...]
Fines, Penalties and Violations! Oh My!
Global data protection regulations (new or updated) are being enforced aggressively, resulting in a tsunami of hefty fines and penalties handed out to violators. The majority of these violations are a result of the failure to conduct regular risk assessments, [...]
Making Ongoing Risk Management an Operational Standard
No business today is 100 percent secure from cyberthreats and more businesses are waking up to this reality now than ever before. It’s no wonder cybersecurity investment in 2020 is pegged to grow by 5.6 percent to reach nearly [...]
Security – Do You Know Your Digital Risk?
Rapid technological advancement and rising global connectivity is reshaping the way the world is functioning. From higher productivity to improved customer satisfaction, technology has played a critical role in the growth of businesses across the world. However, the consequential bad [...]
All You Need to Know About Least Privilege
In IT, the principle of least privilege (PoLP) refers to the concept that any process, program or user must be provided with only the bare minimum privileges (access or permissions) needed to perform a function. For instance, if a [...]
Why Your Business Needs a Data Security Policy
Today, the competitive business environment is data-driven. Data provides key insights into your customers and business performance that helps you make better decisions and improve processes. However, the sudden influx of employees working remotely exposes your organization’s information to [...]
Protecting Your SaaS Data Is Your Responsibility
Businesses worldwide are investing heavily in software-as-a-service (SaaS) or cloud computing solutions in the search for flexible, reliable and affordable software infrastructure. The International Data Corporation (IDC) anticipated the cloud software market to reach $151.6 billion by 2020, but [...]
Data Protection Regulations: The ‘New Normal’ For All Businesses
In today’s global information economy, your business data is the golden goose chased by cybercriminals. Given how this data has an endless life, who can ensure that it isn’t exploited for unsavory gains? Well, governments worldwide have stepped up to [...]
Encryption Explained
The science of encryption has been the answer to the fundamental human need to masquerade and protect sensitive information from prying eyes. Although the technology has witnessed a drastic metamorphosis over the ages, the fundamental concept behind encryption has [...]
Data Privacy Versus Data Security: A Closer Look
The importance of data privacy and data security has grown exponentially as organizations today collect and store more information than ever before. Having a robust data protection strategy is critical to safeguard confidential information and to ensure smooth functioning of [...]
Ensuring Proper and Secure Backups While Working With Remote Workforces
Ever since the COVID-19 pandemic plunged the world into disarray, remote working has become a major tool for businesses to keep their operations up and running. While some organizations already had the technical infrastructure to accommodate remote work, most were [...]
Backup Strategies to Prevent Data Loss
We live in a digital age where data has become one of the most valuable commodities in the world. Businesses collect huge volumes of data every day from their customers, and this data plays a critical role in their [...]
Ransomware: Cybersecurity’s Biggest Bully Yet
Can you imagine logging into your system to access your business data and being unable to do so? Talk about your worst nightmare coming true! Unfortunately, an increasing number of businesses around the world are living this nightmare with [...]
The Dangers of the Inbox
Every now and then, an email with a catchy subject line appears in your inbox and you end up clicking on it, either because you’re curious about the subject line or because you assume the sender is trustworthy. Unfortunately, [...]
How to Ensure Compliance When Working Remotely
The ongoing COVID-19 pandemic has presented businesses across the world with many unique challenges when it comes to their day-to-day operations. With every business trying its best to survive in this unprecedented climate, remote working has become a critical [...]
Ransomware Equals a Data Breach
From a data regulator’s perspective, it is the responsibility of your business to keep data safe from cyber threats, inform clients about a breach within a stipulated period and provide necessary documentation as proof of your efforts. Although different [...]